Recover email password without the stress. Forgetting it happens to everyone, maybe you haven’t logged in for a while, or you recently switched devices and drew a blank. Either way, being locked out of your inbox can feel like hitting a wall.
The good news? There are several tried-and-true ways to get back in. Whether it’s through recovery emails, phone verification, security questions, or built-in provider tools, you’ve got options.
In this guide, I’ll walk you through 5 methods that work to recover your email password, simple, safe, and effective. Ready to get back into your account? Let’s dive in.
The Importance of Proactive Account Recovery Setup
Before diving into the recovery methods, it is essential to understand why the process is designed the way it is. You cannot simply ask a provider to tell you your old password. This is a fundamental security feature that protects your data.
Why You Can’t Just “Ask for Your Password”
Email providers do not store your password in a readable format. They use advanced cryptographic techniques, like hashing and salting, to store a secure, irreversible representation of it. When you enter your password, they perform the same calculation and compare the results. This means even employees of the email provider cannot see your password. Therefore, the only option when you forget it is to go through a secure process to reset it.
Setting the Foundation for Easy Recovery
The entire password recovery system hinges on the information you provide when you set up your account. The two most critical pieces of information are a recovery phone number and a recovery email address. These are your primary lifelines if you get locked out. Taking a few minutes to add and verify this information is the single most important step you can take to prevent future access issues. Think of it as digital insurance for your account.
Method 1: Using a Recovery Email Address
The most common and one of the most reliable methods for password recovery is using a secondary email address. This is an alternate email account that you have previously linked to your main account for security purposes.
How This Method Works
When you initiate the password reset process, the provider gives you the option to send a verification code or a special reset link to your registered recovery email. You then access this alternate inbox, retrieve the code or click the link, and follow the on-screen instructions to create a new password for your main account. This process verifies that you have control over the linked recovery account.
Step-by-Step Guide to Recovery via Email
The general process is consistent across most platforms. First, navigate to the email provider’s login page and enter your email address. Click the “Forgot Password?” or “Trouble signing in?” link. The system will then present you with your available recovery options. Select the option to send a code to your recovery email. Next, log in to your alternate email account, find the message from your provider, and copy the numeric code. Return to the recovery page, enter the code, and you will be prompted to set a new, secure password.
Choosing a Secure and Reliable Recovery Email
Your recovery email is a powerful key to your main account, so it must be secure. Choose an alternate email address that you access regularly and have also secured with a strong password and two-factor authentication. Avoid using an old, neglected account, as you may lose access to it as well.
Method 2: Verifying with a Recovery Phone Number
Using a phone number is an excellent recovery method because it connects your digital identity to a physical device you own. This is a form of two-factor authentication, combining something you know (your email address) with something you have (your phone).
The Role of Your Phone in Account Security
A registered phone number is a direct and immediate way for an email provider to communicate with you. Because mobile numbers are unique and generally tied to an individual, they serve as a strong proof of identity. Most modern email services heavily encourage users to add a phone number for this reason.
Recovering via SMS or Phone Call
The recovery process via phone is similar to the email method. After clicking “Forgot Password?”, you can choose to have a verification code sent to your phone. You will typically have two choices: receiving the code as a text message (SMS) or through an automated phone call. Once you receive the code, you enter it on the recovery webpage to verify your identity and proceed to set a new password.
What to Do If You Change Your Phone Number
It is critically important to keep your recovery information up to date. If you get a new phone number, one of the first things you should do is update it in your email account’s security settings. Forgetting to do so is a common reason why people get permanently locked out of their accounts.
Method 3: Answering Security Questions
Security questions were once a standard recovery method, though they are becoming less common today due to potential vulnerabilities. This method involves answering personal questions that you previously set up.
The Traditional but Risky Method
The system works by asking you one or more questions you answered when setting up your account, such as “What was the name of your first pet?” or “What city were you born in?”. If you provide the correct answers, the system grants you access to reset your password. The primary risk is that the answers to these questions can often be found through social media or public records, making them guessable by a determined attacker.
Best Practices for Security Questions
If you must use security questions, choose questions whose answers are not public knowledge. The best answers are memorable to you but known by no one else. For added security, some experts recommend providing a false but memorable answer. For example, if the question is “What is your mother’s maiden name?”, your answer could be “Mickey Mouse” instead of the real name. This makes it impossible for someone to guess, as long as you can remember the fabricated answer.
Method 4: Using Device-Based Verification
A more modern and highly secure recovery method involves using a trusted device where you are already logged into your account. This is a common feature for providers like Google and Microsoft.
How Modern Services Verify Your Identity
If you are logged into your email account on your smartphone, for example, the recovery process can use that device for verification. When you try to reset your password from a new computer, the provider will send a notification or prompt directly to your trusted phone. This prompt will ask, “Are you trying to sign in?” You simply need to tap “Yes, it’s me” on your phone to approve the sign-in and proceed with the password reset.
The Benefits of Device Prompts
This method offers excellent security because it requires physical access to your trusted device. It is also incredibly convenient, as it eliminates the need to receive and type in codes. It smoothly confirms your identity in a single tap, making it one of the easiest and safest ways to recover an account.
Method 5: The Last Resort – The Account Recovery Form
When all other automated methods fail, most providers offer a manual account recovery form as a final option. This is the most intensive and time-consuming method, reserved for situations where you have lost access to your recovery email and phone.
When All Other Methods Fail
The account recovery form is a detailed questionnaire designed to prove your ownership of the account through knowledge-based information. You will be asked to provide details such as your account creation date, previous passwords you have used, email addresses of people you frequently contact, and the names of any custom folders or labels you have created.
Tips for Successfully Completing the Form
To increase your chances of success, fill out the form from a computer and location (like your home or office) that you have used to access the account before. Be as precise as possible with your answers. If you are unsure of an exact date, provide your best guess. After submitting the form, the provider’s support team will manually review your answers, which can take several days.
Platform-Specific Password Reset Guides
While the general methods are similar, each email provider has a unique interface for its recovery process. Navigating these specific workflows is the final step in regaining access.
How to Change Gmail Password
After successfully recovering your Google account, your first action should be to set a new, strong password. Gmail’s security settings provide a straightforward process for this.
A Guide to Resetting Outlook Password
Microsoft’s account recovery portal guides users through a clear, step-by-step process. It leverages all the modern methods, including app-based verification and device prompts.
Steps to Reset Yahoo Password
Yahoo has been a major email provider for decades, and its recovery system is well-established. For a deeper look into the platform, a Yahoo Mail overview is available.
The Forgot AOL Password Reset Process
As another long-standing service, AOL provides a familiar password reset process. Its history and features are covered in more detail in this AOL Mail overview.
Beyond Recovery: Building Strong Password Habits
Regaining access to your account is the immediate goal, but preventing the problem from happening again is just as important. Adopting strong password and security habits is the key to long-term account safety.
A Checklist for a Secure Email Account
This checklist outlines the fundamental practices for maintaining a secure email account. Integrating these habits into your digital routine can significantly reduce your risk of getting locked out or compromised.
- Create Strong Passwords: Use a long combination of uppercase and lowercase letters, numbers, and symbols. Avoid using personal information.
- Enable Two-Factor Authentication (2FA): This provides a critical second layer of security, usually involving a code from your phone.
- Use a Password Manager: These tools create and store highly complex, unique passwords for all your accounts, so you only have to remember one master password.
- Review Recovery Information Regularly: Check your recovery phone number and email address at least once a year to ensure they are up to date.
- Beware of Phishing: Never enter your password after clicking a link in an email. Always navigate directly to the website yourself.
The Role of Inbox Management in Security
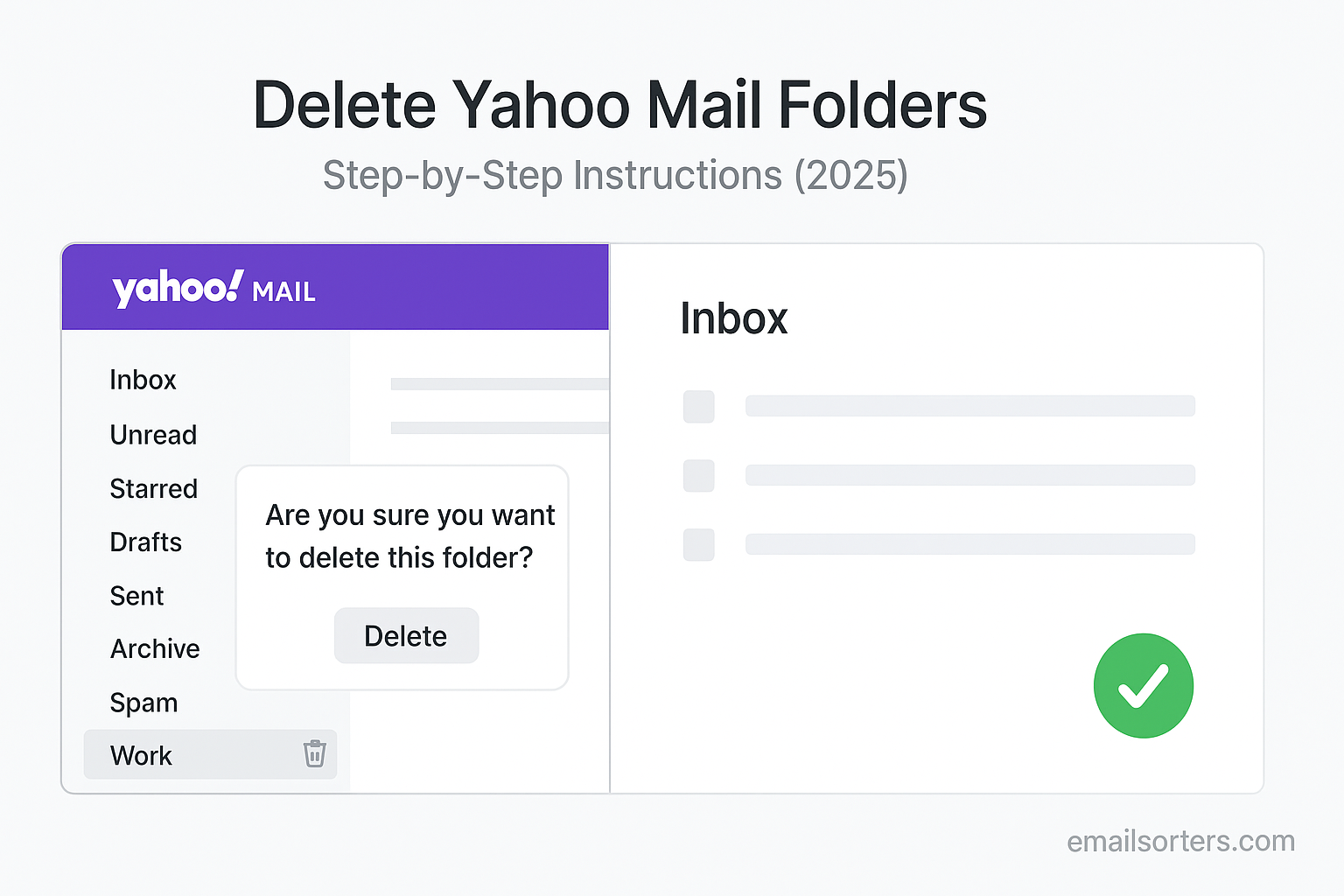
A well-organized inbox is not just about productivity; it is also a component of good security. Clutter can hide threats, and old emails can contain sensitive information that could be exposed in a data breach.
Keeping Your Digital Space Clean
Regularly deleting or archiving old emails reduces the amount of data that could be compromised if your account is ever breached. This practice, known as digital hygiene, minimizes your risk profile over time.
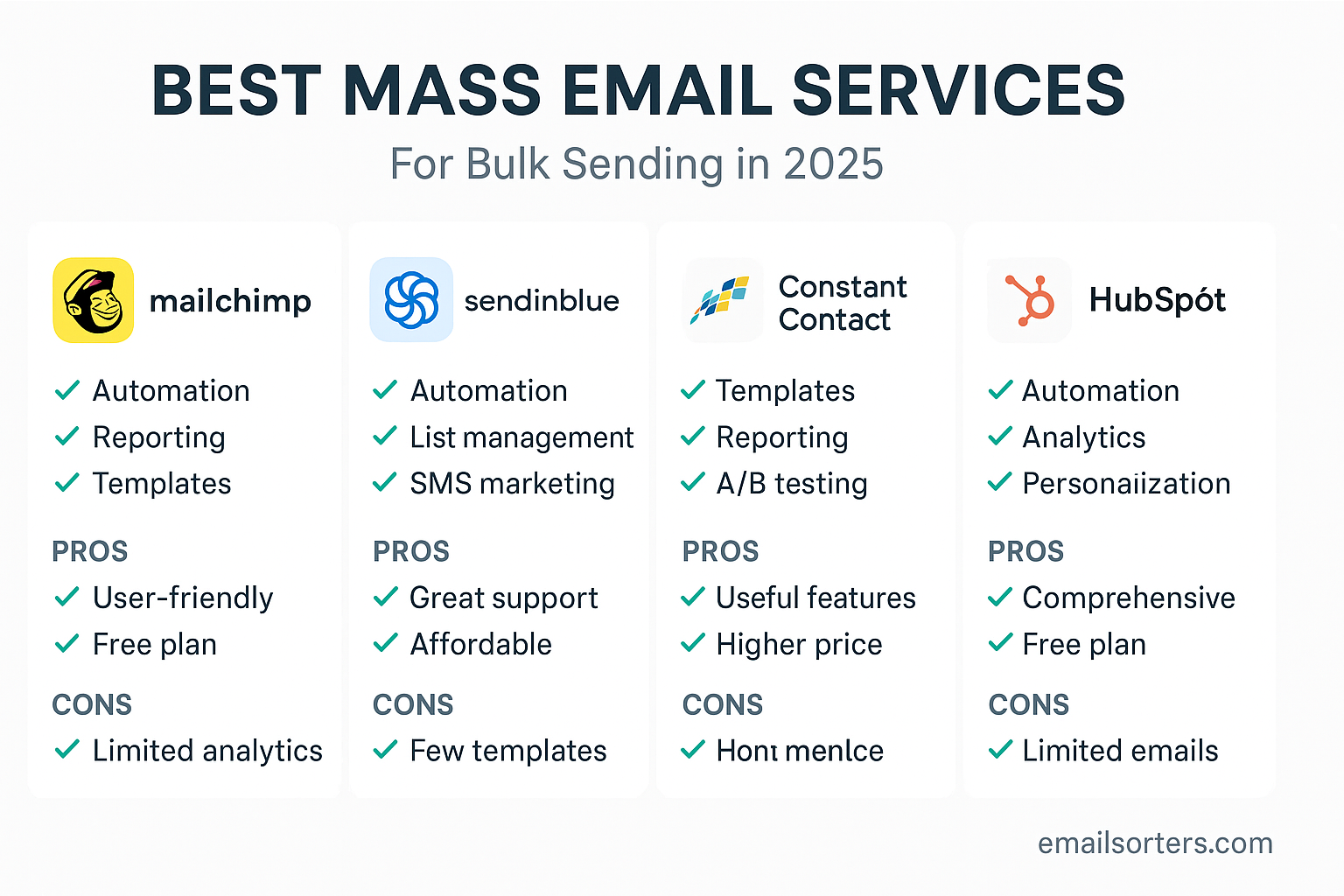
Using Tools for a Safer Inbox
For users with thousands of messages, manual cleaning is impractical. Third-party inbox management tools can help automate this process. Services from companies like Clean Email, for example, offer features to intelligently sort, group, and bulk-delete emails, helping to maintain a safer and more organized digital space.
Conclusion
Losing access to your email account can be a stressful experience, but the recovery methods provided by modern email services are effective and secure. Whether you use a recovery email, a phone number, a device prompt, security questions, or a manual recovery form, there is almost always a path back into your account. However, the best strategy is always prevention. By setting up your recovery options in advance, using a strong and unique password, and enabling two-factor authentication, you can transform your email account into a secure fortress and ensure you never lose the keys again.